Detect RAG Pipeline Poisoning Before It Reaches AI Outputs
Gain visibility into how data moves through RAG pipelines, from source documents and connectors to embeddings, vector databases, retrievers, prompts, and model responses. Grafyn helps security teams detect poisoned content, risky retrieval paths, and compromised knowledge sources before they influence enterprise AI behavior.
RAG Pipelines Are Becoming a New Poisoning Attack Surface
RAG systems rely on trusted knowledge sources to answer questions, summarize documents, support employees, and power enterprise copilots. But when attackers or insiders manipulate source documents, metadata, embeddings, vector stores, or retrieval logic, poisoned content can surface as trusted AI output. For CISOs, the challenge is knowing what data entered the pipeline, which sources influenced the response, and how far compromised knowledge can spread.
1
Poisoning a single document can influence RAG outputs.
25%
Enterprise GenAI apps are expected to face repeated security incidents.
40%+
AI-related data breaches are expected to stem from improper GenAI use.
90%
RAG poisoning attacks have achieved high success rates in research settings.
A Complete Solution to Detect and Reduce RAG Poisoning Risk
Grafyn helps security teams map RAG pipelines across source systems, connectors, embeddings, vector databases, retrievers, prompts, and outputs so they can detect poisoning risk and reduce the impact of compromised retrieval.
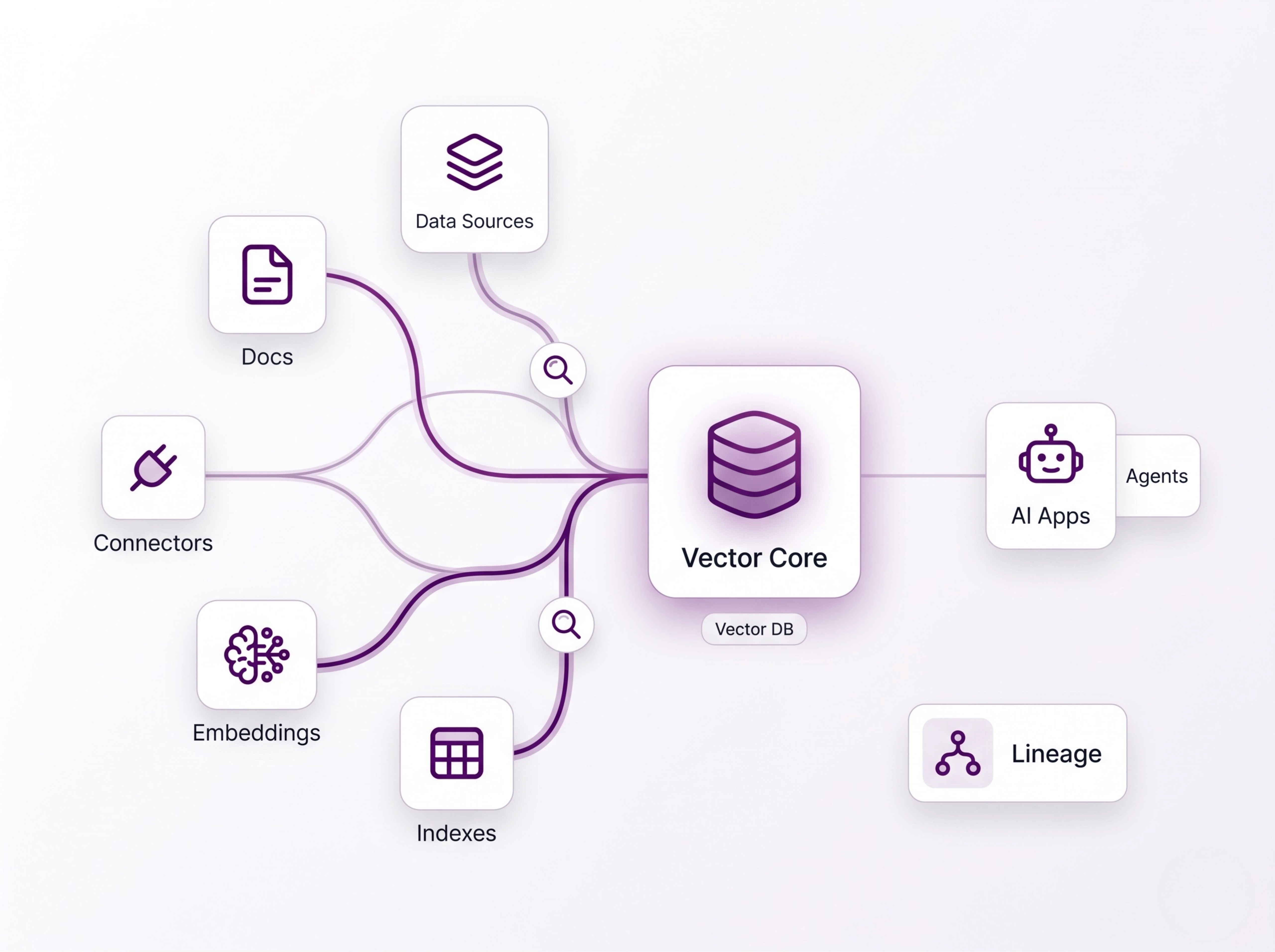
Map RAG and Vector Data Lineage
Discover which documents, data sources, connectors, embeddings, vector databases, indexes, and retrieval paths feed enterprise AI applications, agents, and copilots.
.png)
Detect Poisoned Knowledge and Vector Stores
Identify manipulated documents, suspicious metadata, unauthorized content changes, poisoned embeddings, compromised vector records, risky indexes, and retrieval anomalies that could influence model responses.
.png)
Reduce RAG and Vector DB Poisoning
Trace which AI applications, agents, users, and workflows depend on compromised documents, embeddings, or vector database entries, then contain affected sources, restrict risky retrieval paths, and restore trusted context.
.svg)