Stop AI Attacks
Before They Spread
Grafyn’s Threat Detection & Response offering helps enterprises identify attacks, misuse, and anomalous behavior across the AI ecosystem in real time. By continuously monitoring models, agents, and AI-driven workflows, security teams can uncover suspicious activity early, accelerate investigation, and contain threats before impact spreads.
DemoChallenges
As AI systems become more autonomous, connected, and deeply embedded in enterprise workflows, they create new opportunities for attack, misuse, and operational disruption. Without continuous monitoring and response, organizations struggle to identify threats early, investigate suspicious activity, and contain impact before it spreads.

Delayed Threat Detection
AI attacks often appear as subtle behavior changes, abnormal tool usage, or suspicious access. Without detection, these signals are easy to miss until damage is underway.

Limited Attack Context
When suspicious activity is detected, teams often lack the context to understand what happened and which assets were affected. This delays investigation and response.

Insufficient Defenses
AI threats evolve quickly, from model stealing to agent misuse. Without proactive defenses, organizations remain exposed to attacks they are not ready to stop.
Introducing
Threat Detection & Response
Grafyn’s Threat Detection & Response offering helps enterprises detect malicious behavior, investigate suspicious AI activity, and respond before attacks escalate. By combining continuous monitoring, AI red teaming, investigation workflows, and real-time response, security teams can strengthen defenses and reduce the impact of AI-driven threats across the enterprise.
Key Capablities
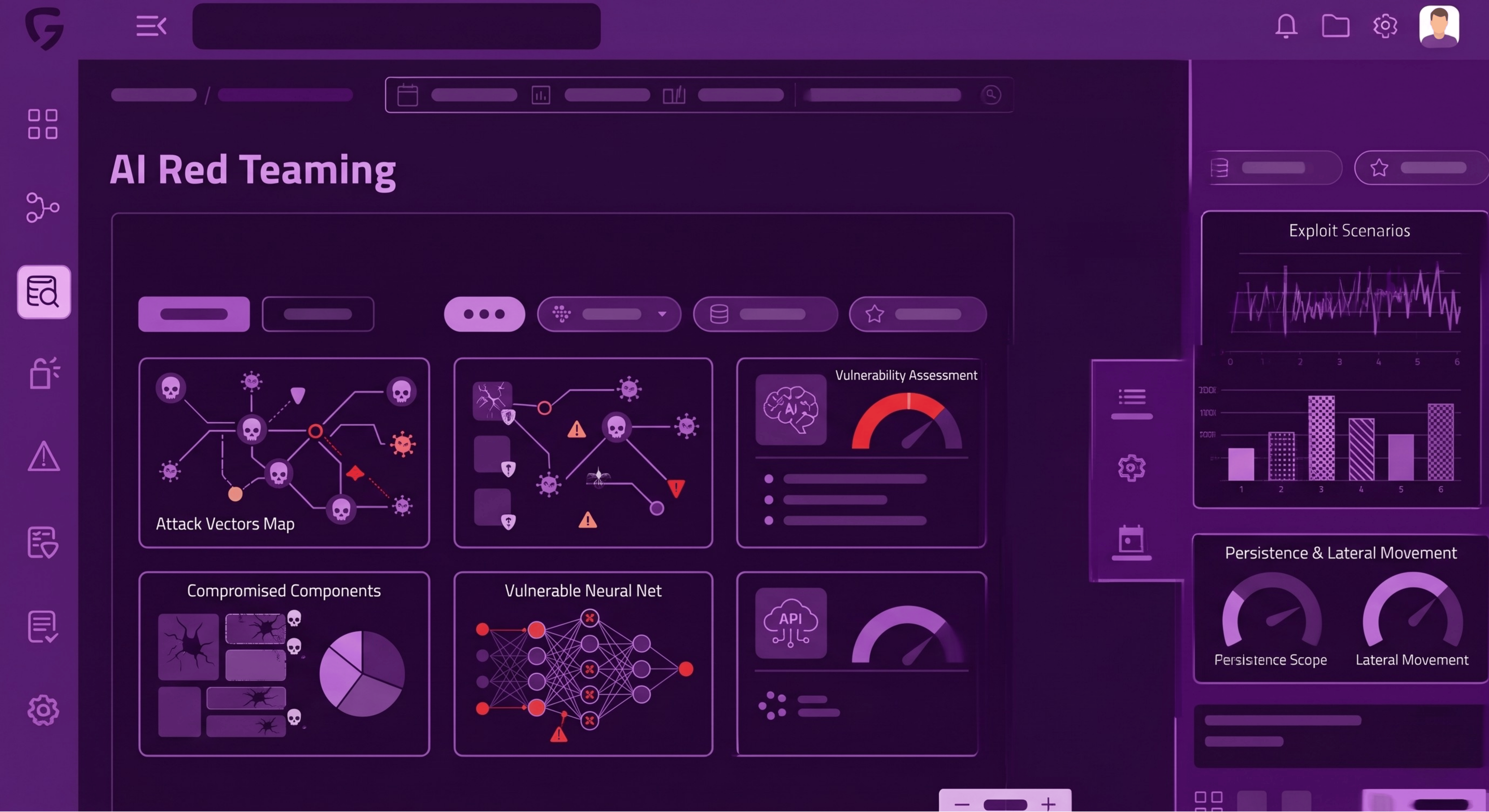
Red Teaming
Test AI systems against realistic attack scenarios to uncover weaknesses before adversaries exploit them.
- Simulate prompt injection, jailbreaks, data exfiltration, and agent misuse scenarios
- Validate how models, agents, and workflows behave under adversarial conditions
- Identify weaknesses in guardrails, tool access, and trust boundaries
- Strengthen AI defenses through continuous security testing and validation
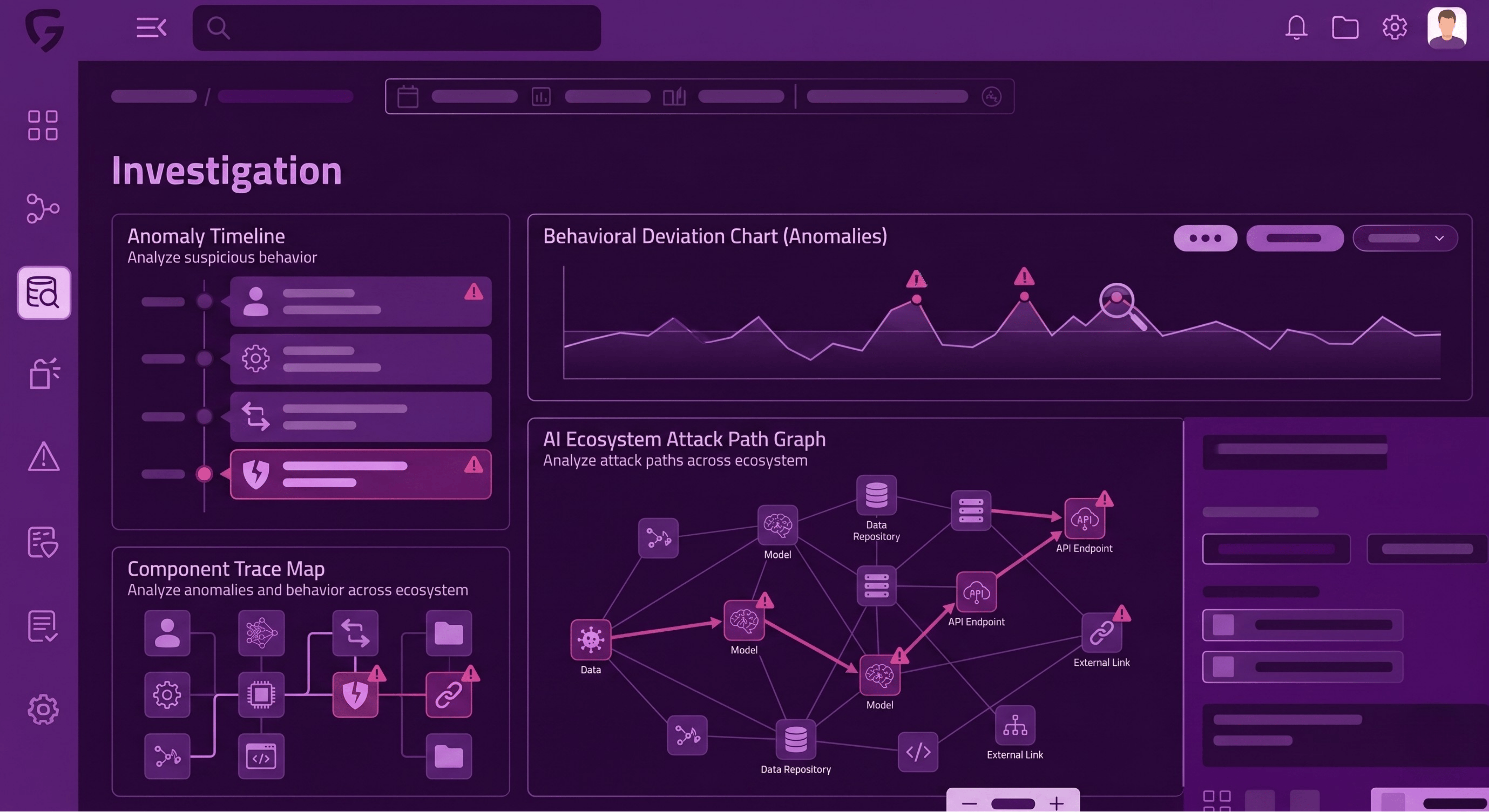
Investigation
Analyze suspicious behavior, anomalies, and attack paths across the AI ecosystem.
- Investigate abnormal prompts, outputs, tool usage, and access activity
- Reconstruct attack paths across models, agents, identities, and connected systems
- Understand which assets, data, and workflows were affected
- Accelerate triage with context-rich analysis of suspicious AI behavior
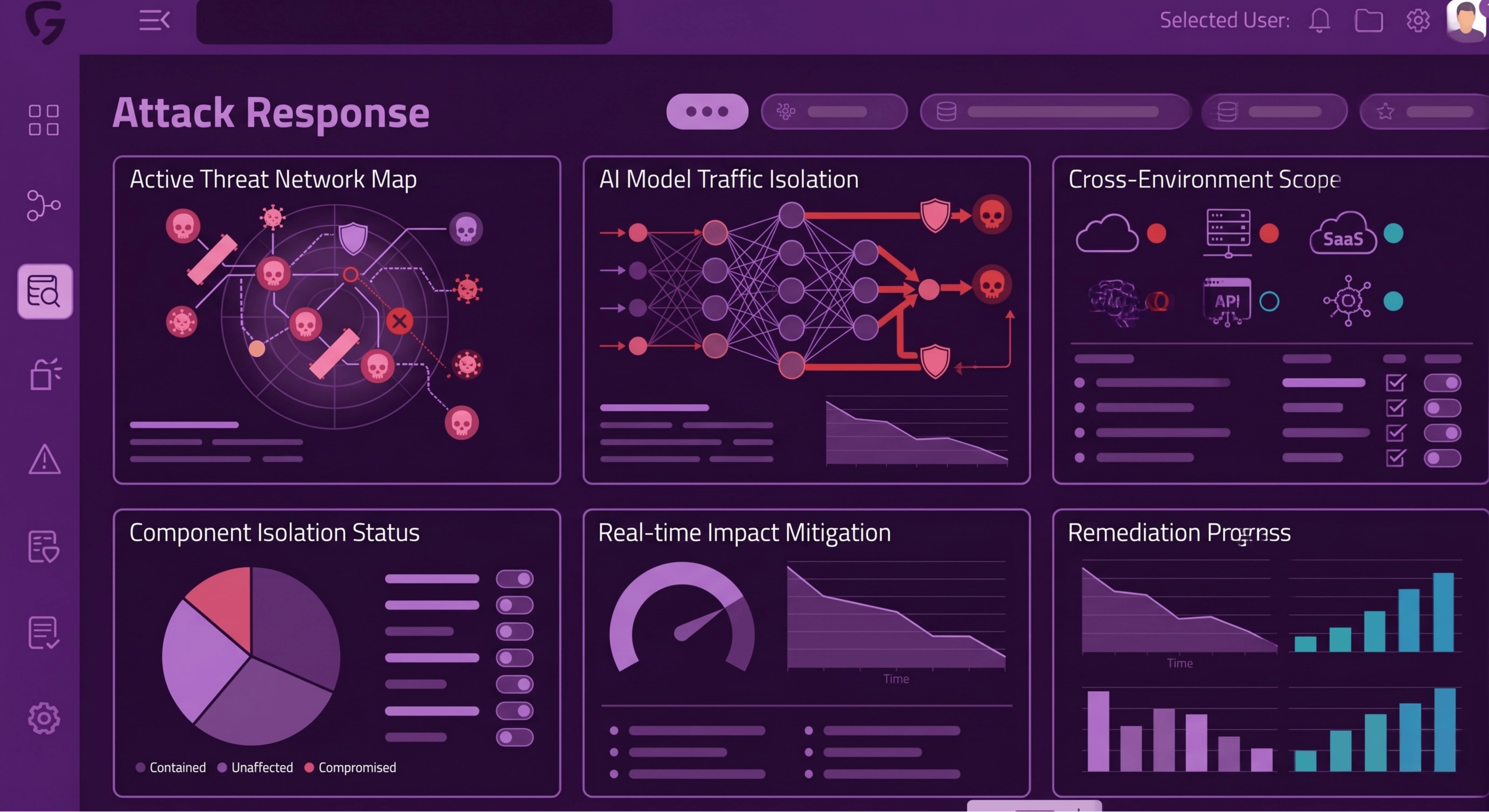
Attack Response
Contain threats and reduce impact in real time across AI systems and connected environments.
- Trigger response actions to isolate affected AI assets and workflows
- Limit malicious access to data, tools, identities, and downstream systems
- Support faster containment of attacks, misuse, and policy violations
- Reduce operational and security impact through coordinated response actions
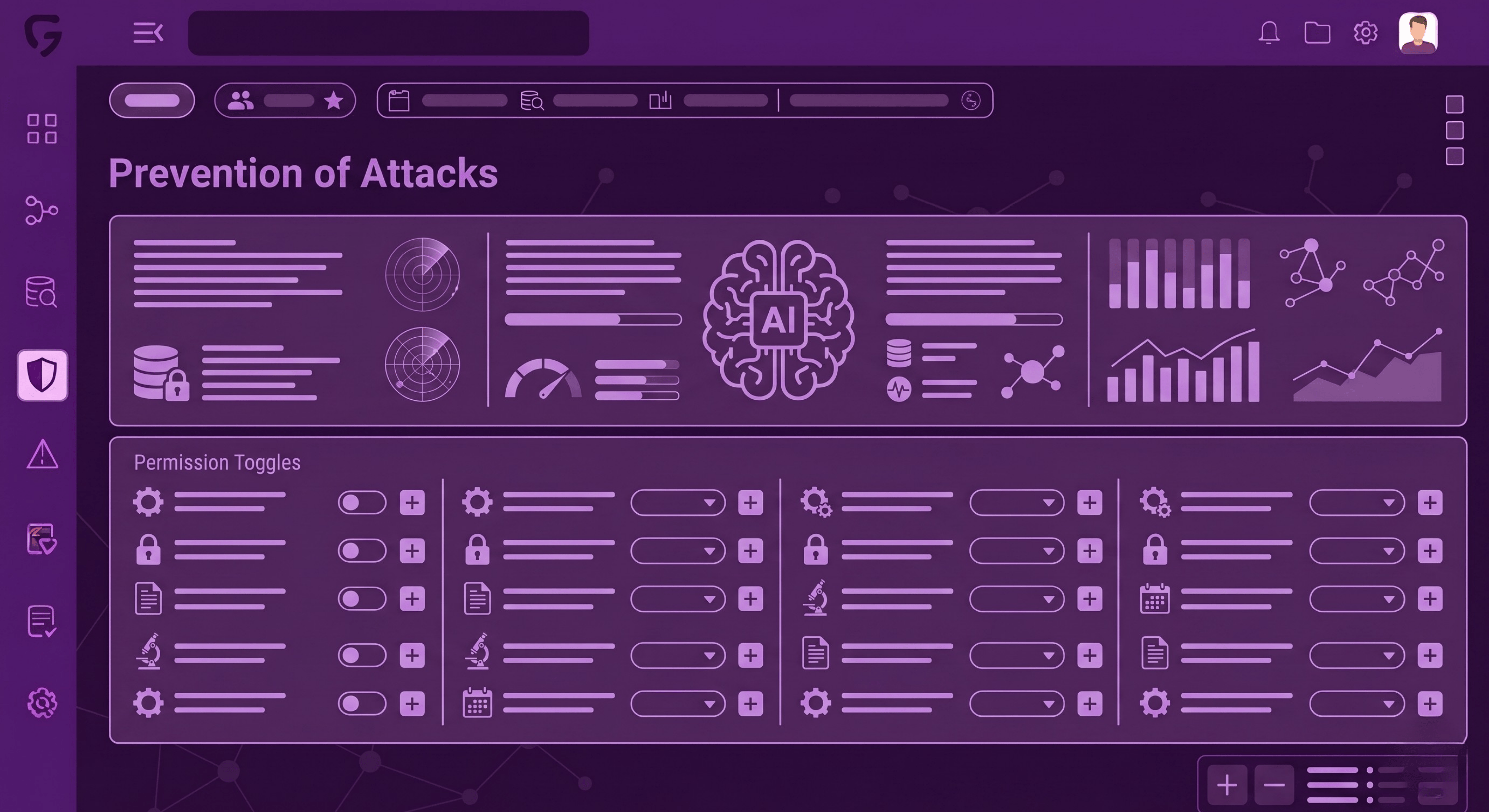
Prevention of Attacks
Strengthen defenses to stop AI attacks before they spread across the enterprise.
- Identify recurring weaknesses exposed through runtime detections and red teaming
- Harden policies, permissions, and trust boundaries around AI assets
- Improve guardrails for models, agents, prompts, and tool usage
- Reduce the likelihood of repeat attacks through continuous defensive improvement

.svg)