Know Your AI Ecosystem
Grafyn’s Discovery & Visibility offering helps enterprises uncover AI assets across cloud, code, SaaS, third-party LLMs, and shadow AI. By mapping how they connect to data, identities, and systems, security teams gain the foundation for posture assessment, blast radius analysis, and threat detection.
DemoChallenges
As AI adoption accelerates, organizations are struggling to keep up with what is being used, how it is connected, and whether it is creating new risk. Without continuous discovery and visibility, hidden AI assets remain unmanaged, their relationships stay unclear, and their risk posture is difficult to assess.

Shadow AI Blind Spots
Employees are using AI tools, copilots, and agents outside approved workflows. This creates blind spots around usage, data exposure, and access.

Unseen Exposure Paths
Organizations often cannot see how AI assets connect to sensitive data, identities, systems, and external services. Without lineage, risk paths remain undetected.

Evolving AI Risk Posture
AI risk changes as behavior, access, integrations, and data usage evolve. Without continuous visibility, these shifts are difficult to detect and assess.
Introducing
Discovery & Visibility
Gain continuous visibility into AI assets, their connections, and their evolving risk posture. Uncover hidden and shadow AI, map how models and agents interact with data, identities, and systems, and establish the foundation for posture assessment, blast radius analysis, and threat detection.
Key Capablities
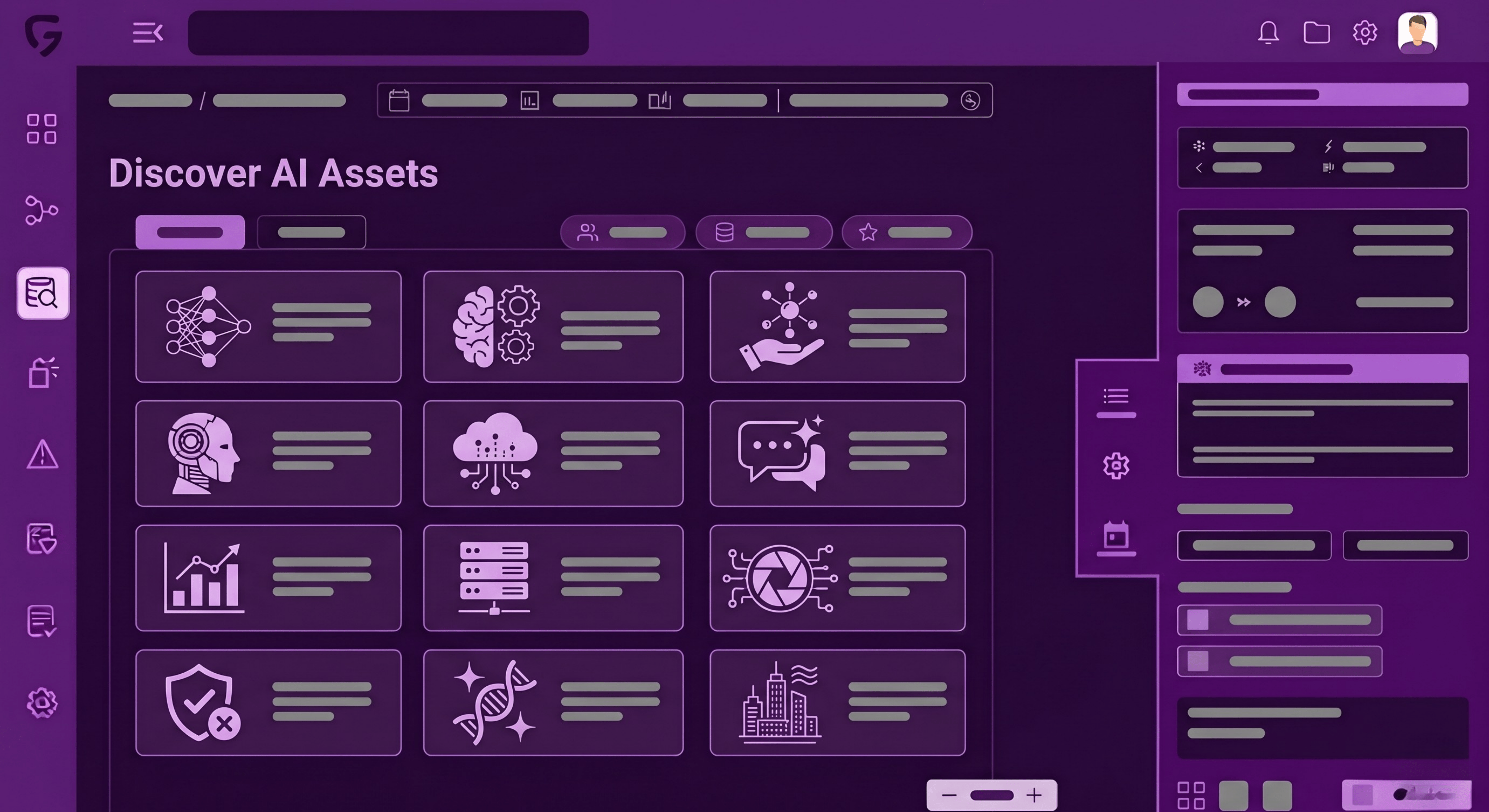
Discovery
Discover AI assets across cloud, code, SaaS, and shadow AI. Build a real-time inventory of models, agents, and third-party AI integrations across the enterprise.
- Uncover sanctioned and unsanctioned AI assets across the environment
- Identify models, agents, identities, MCP servers, vector databases, and AI workflows
- Detect third-party LLM usage, copilots, and shadow AI adoption by employees
- Maintain a continuously updated inventory of the enterprise AI ecosystem
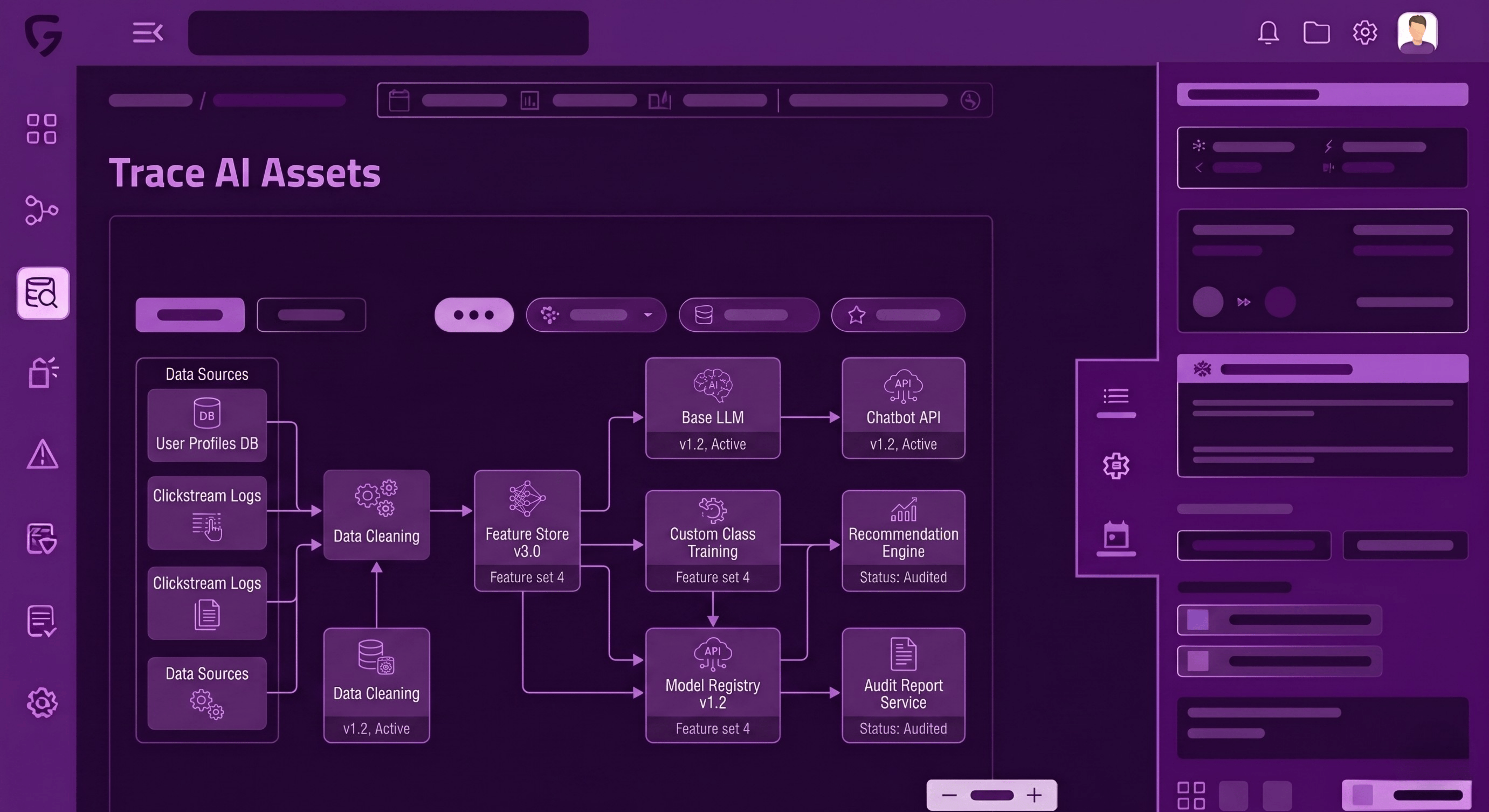
Lineage
Trace how AI assets connect to data, identities, tools, and systems. Understand dependencies, trust boundaries, and exposure paths across the AI ecosystem.
- Map relationships between AI assets, users, identities, and data sources
- Track how sensitive data, outputs, and actions flow across systems
- Reveal dependencies on MCPs, tools, and downstream workflows
- Expose trust boundaries and hidden paths of potential risk propagation
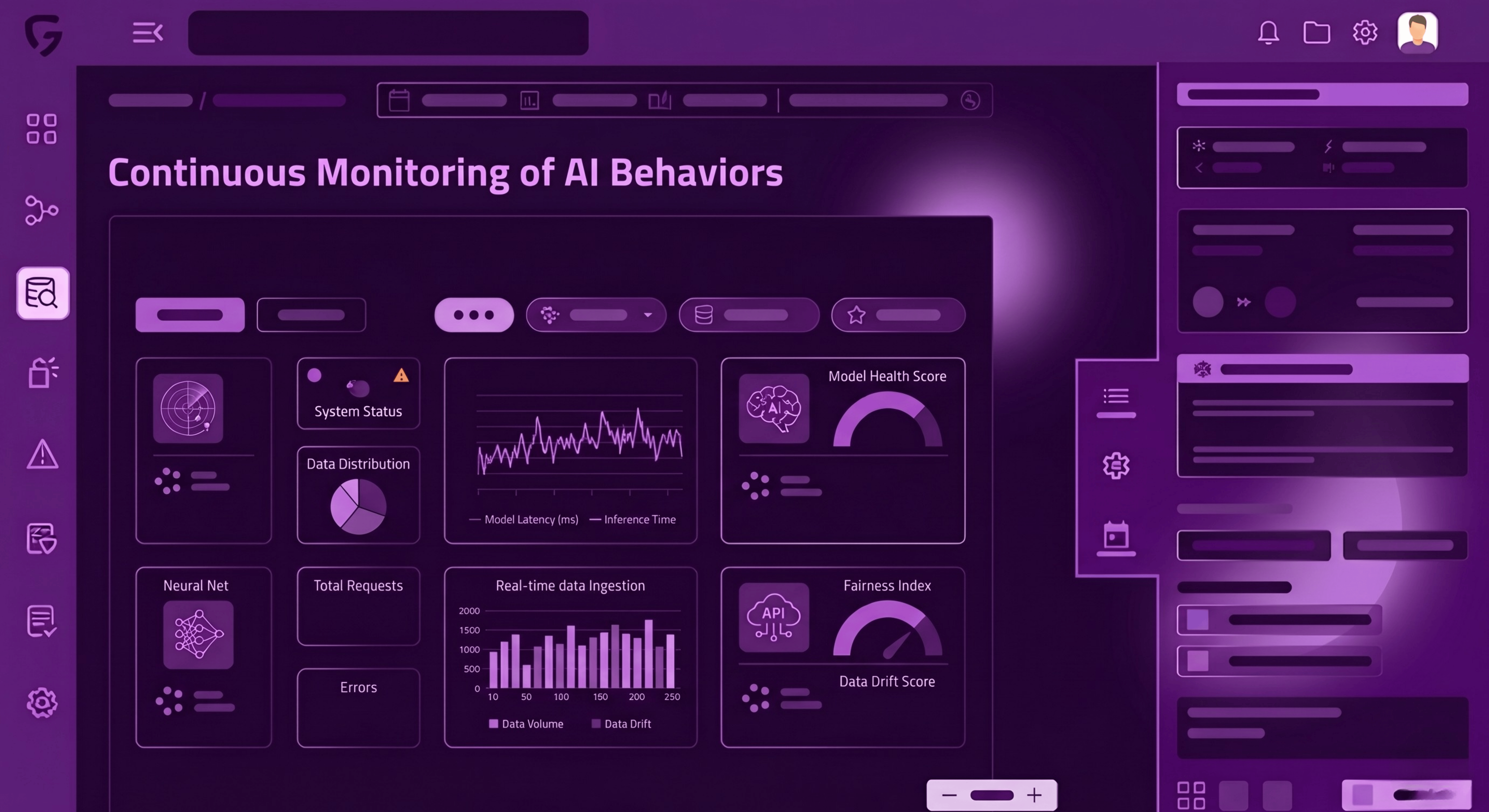
Observability
Continuously monitor AI behavior, usage patterns, performance, and changes over time. Detect drift, misuse, abnormal activity, and performance issues before risk escalates.
- Observe runtime behavior across models, agents, and AI workflows
- Detect unusual access patterns, prompt activity, and tool usage
- Monitor performance, reliability, latency, and operational changes
- Surface early indicators of drift, policy violations, or emerging threats
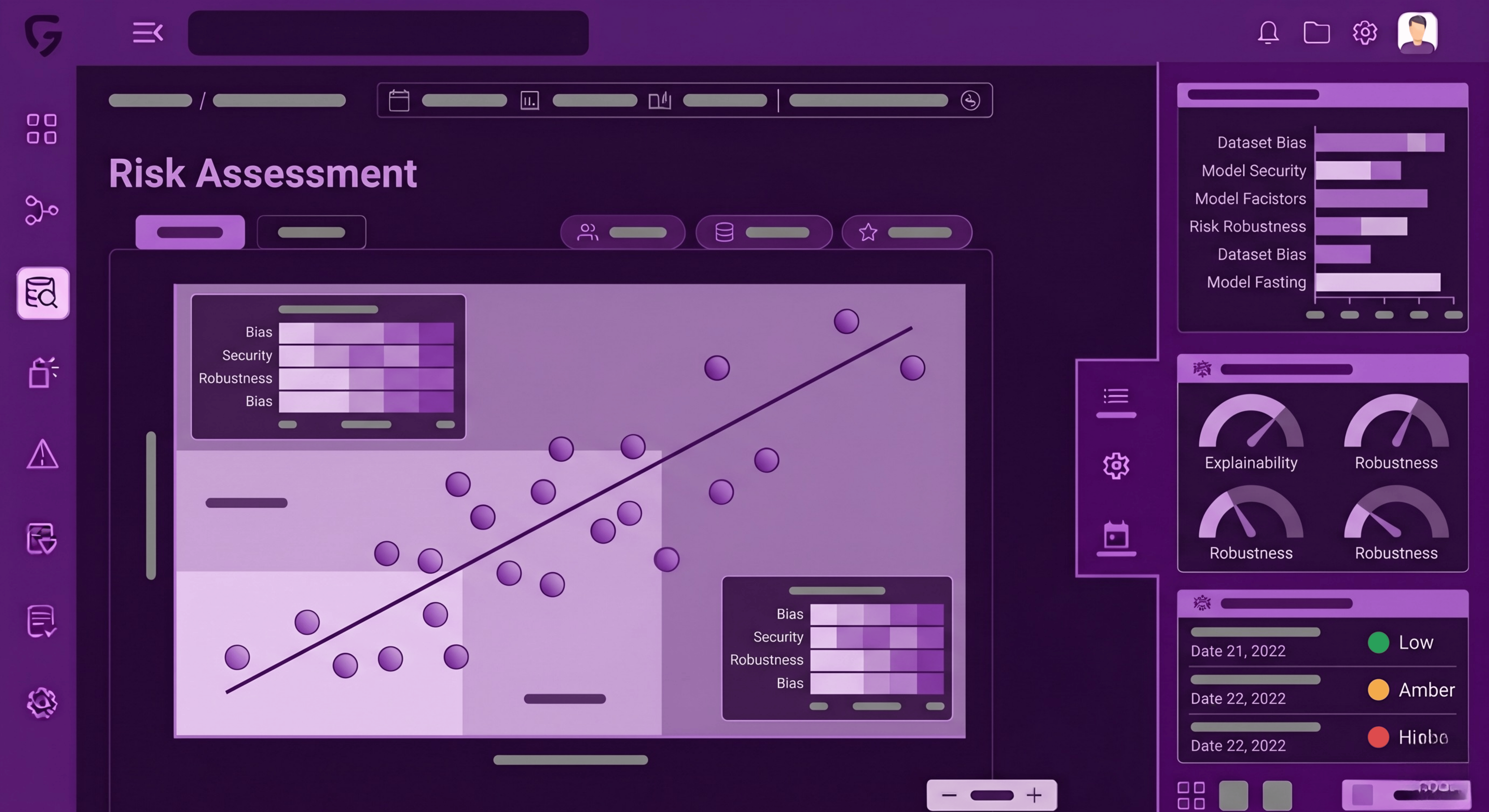
Risk Assessment
Evaluate the risk posture of each AI asset based on exposure, behavior, access, and business impact. Prioritize the risks that matter most.
- Assess AI assets based on data sensitivity and identity exposure
- Analyze risk created by permissions, integrations, and connectivity
- Prioritize high-impact assets based on business and security context
- Provide evidence for elevated risk across sensitivity, access, behavior, and performance

.svg)