Red Team AI Agents Before They Act on Enterprise Systems
Gain visibility into how AI agents can be manipulated, hijacked, or misused across tools, identities, APIs, MCP servers, workflows, and business applications. Grafyn helps security teams test agentic AI systems before attackers exploit prompt injection, tool misuse, privilege abuse, data exposure, or unsafe autonomous actions.
AI Agents Are Creating New Security Blind Spots
Unlike chatbots, AI agents do not just generate responses. They can reason, call tools, access data, trigger workflows, interact with APIs, and take actions across enterprise systems. That creates a new security challenge for CISOs: understanding whether an agent can be manipulated, over-permissioned, tricked into exposing data, or used to perform unauthorized actions before it reaches production.
50%
of enterprise incident responses are predicted to involve AI-driven applications by 2028.
25%
of enterprise GenAI applications are predicted to experience at least five minor security incidents per year by 2028.
15%
of daily business decisions are expected to be made autonomously by agentic AI by 2028.
33%
of enterprise software applications are expected to include agentic AI by 2028.
A Complete Solution to Test and Secure Agentic AI Systems
Grafyn helps security teams red team AI agents across the full agentic workflow, from prompts and memory to tool calls, permissions, MCP connections, APIs, outputs, and downstream actions.
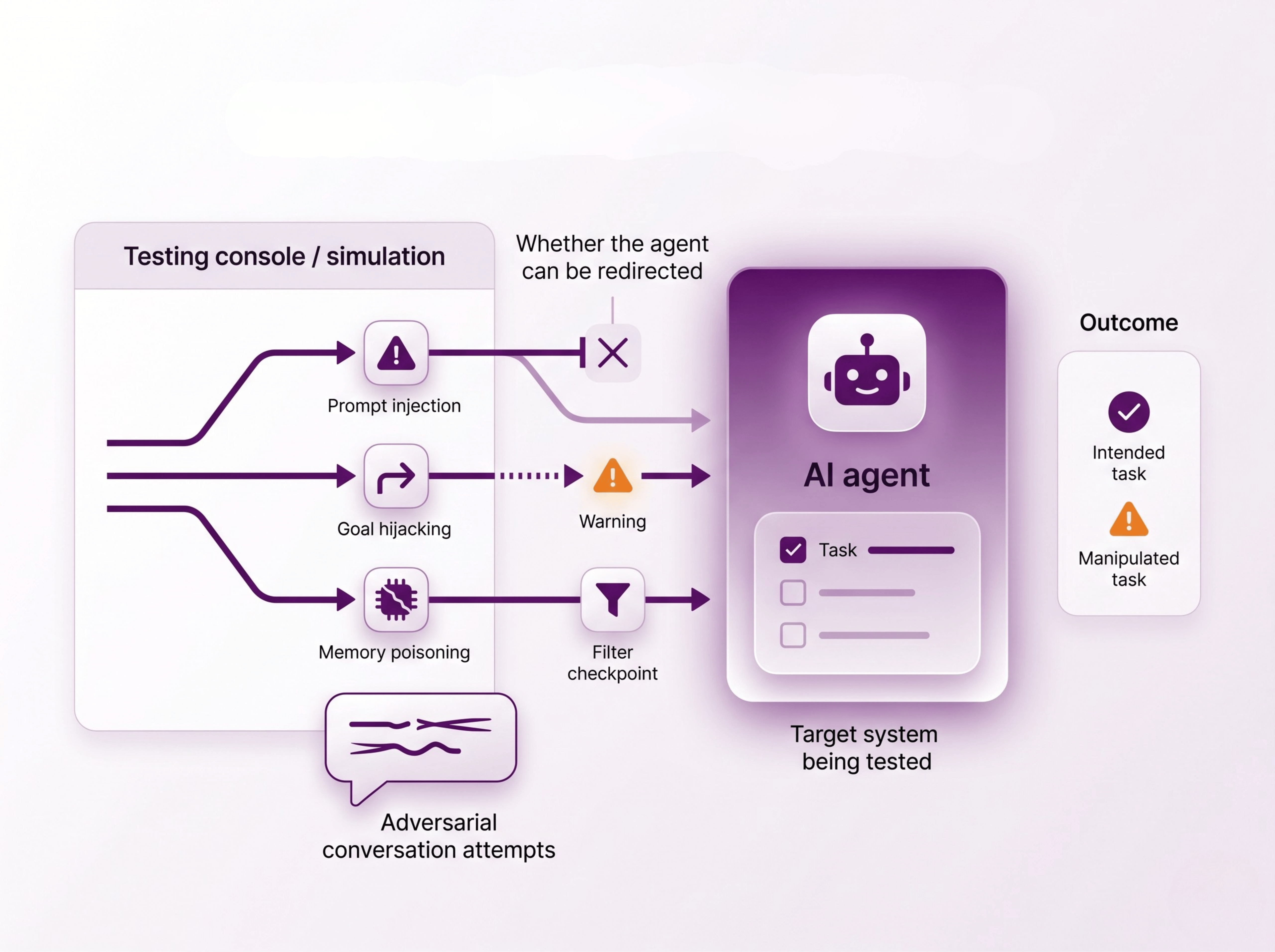
Test for Agent Manipulation
Simulate prompt injection, goal hijacking, malicious instructions, memory poisoning, and adversarial conversations to understand whether an agent can be redirected away from its intended task.
.png)
Validate Tool and Permission Abuse
Assess whether agents can misuse tools, overreach permissions, access sensitive systems, call unauthorized APIs, or execute actions beyond approved trust boundaries.
.png)
Detect Unsafe Autonomous Actions
Test whether agents can expose sensitive data, trigger risky workflows, make unauthorized changes, or perform harmful actions across connected enterprise systems before deployment.
.svg)