Minimize How Far
AI Compromise Could Spread
When AI is compromised, the real question is how far the damage can spread. Grafyn maps how AI connects to sensitive data, identities, actions, tools, and environments, helping security teams quantify exposure and uncover high-risk propagation paths. This enables teams to reduce downstream impact and contain risk before incidents escalate.
DemoChallenges
As AI systems gain access to more data, identities, tools, and environments, a single compromised or misused asset can create outsized consequences. Without a clear understanding of blast radius, organizations struggle to measure how far exposure can spread and which risks require immediate containment.

Unbounded Data Exposure
AI assets often access sensitive data, knowledge stores, and outputs beyond their intended scope. This makes it difficult to determine how much data could be exposed during misuse or compromise.

Inherited Identity Chains
AI systems often operate with inherited permissions, linked identities, and tool access across systems. Without understanding the chain, compromise can spread beyond the original asset.

Evolving Trust Boundaries
AI workflows increasingly span internal systems, third-party tools, and external services. As trust boundaries expand, organizations struggle to determine how compromise could spread across them.
Introducing
Blast Radius Detection & Minimization
Understand how far AI compromise could spread across data, identities, actions, and trust boundaries. Quantify downstream exposure by analyzing the reach of each AI asset and the dependencies connected to it. Identify high-impact propagation paths and prioritize containment to reduce blast radius before risk escalates.
Key Capablities
Data Radius
Understand how much sensitive data an AI asset can access, influence, or expose across the enterprise.
- Identify the sensitive data stores, prompts, outputs, and knowledge sources an AI asset can reach
- Measure direct and indirect exposure to enterprise data across connected systems
- Reveal data access paths that increase the impact of compromise or misuse
- Quantify how far sensitive data exposure can spread from a single AI asset

Identity Radius
Determine which identities, permissions, and privileges an AI asset can inherit, invoke, or misuse.
- Map linked identities across users, service accounts, agents, and AI workflows
- Analyze inherited permissions and privilege paths connected to each AI asset
- Reveal over-permissioned access that expands compromise impact
- Understand how identity relationships amplify blast radius across the environment
.png)
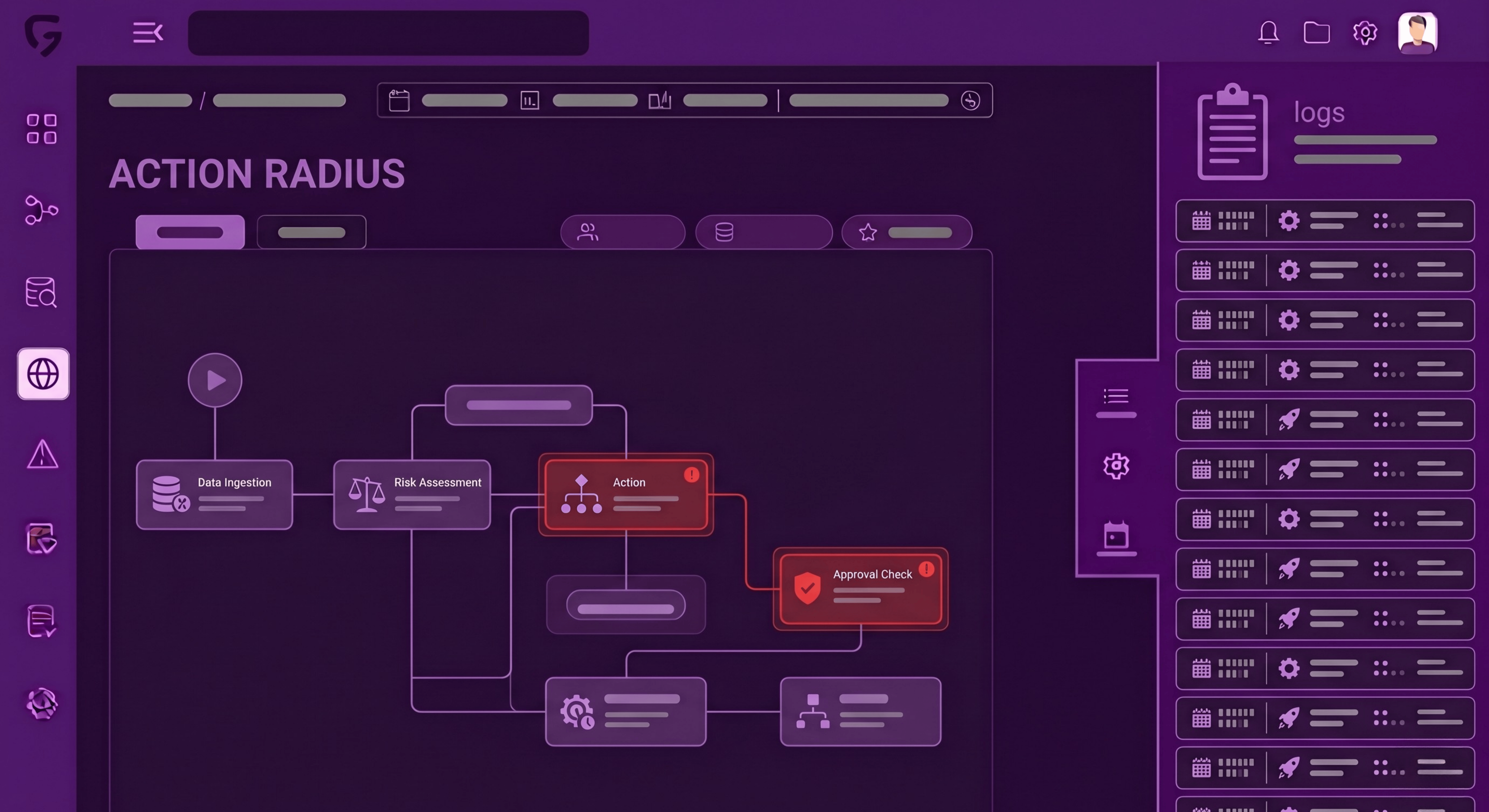
Action Radius
See what actions, systems, and downstream workflows an AI asset can trigger, modify, or influence.
- Identify tools, APIs, and enterprise systems reachable by each AI asset
- Trace the downstream actions an AI workflow can initiate or alter
- Measure how compromise could propagate through automated decisions and system changes
- Expose high-impact action paths that increase operational risk
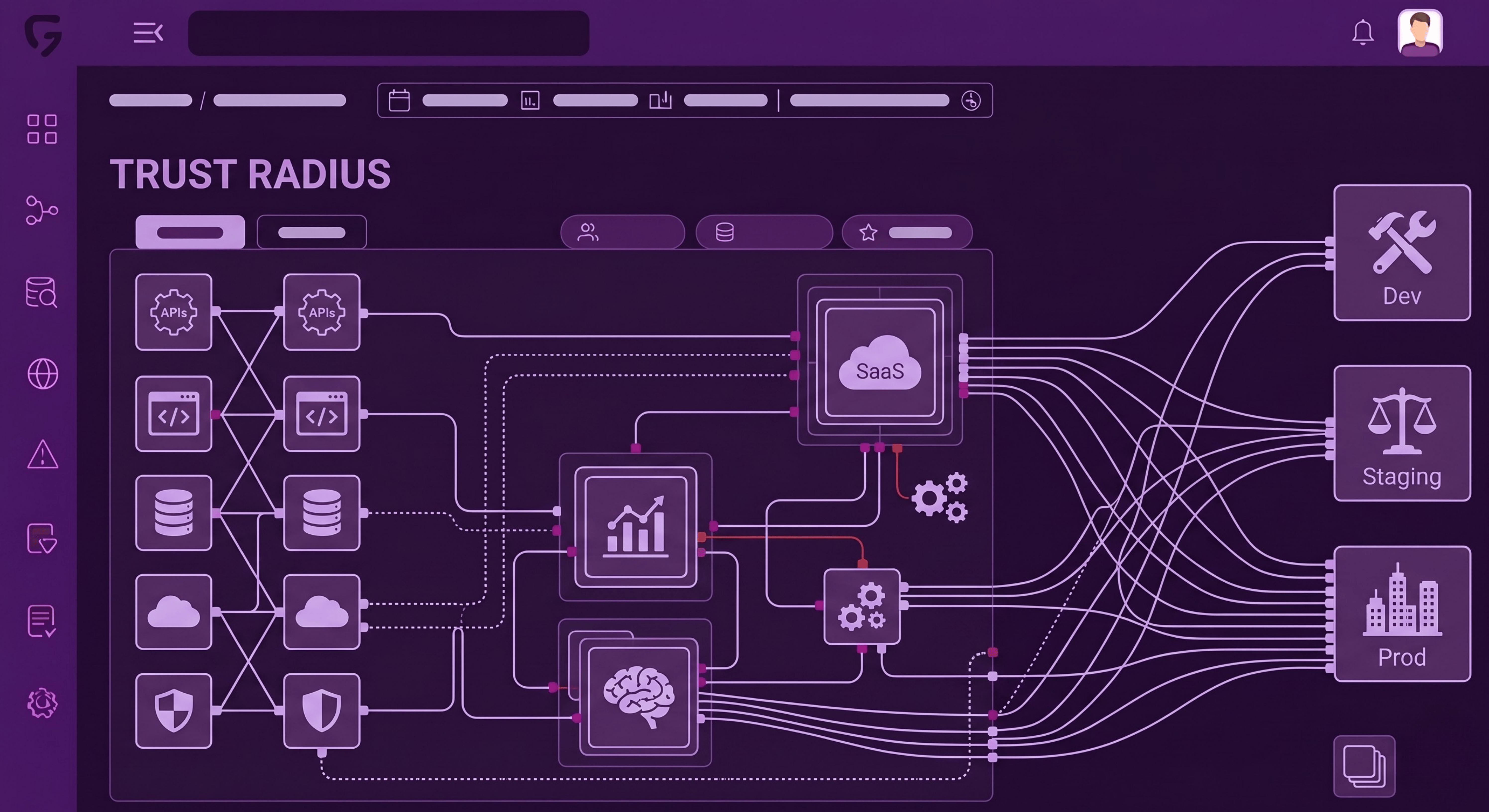
Trust Radius
Understand how widely an AI asset can extend across tools, services, and environments through connected trust relationships.
- Map the tools, platforms, and environments an AI asset can traverse
- Reveal trust boundaries across internal systems, SaaS platforms, and external services
- Identify cross-environment dependencies that increase the spread of compromise
- Measure how broadly risk can propagate through connected AI ecosystems

.svg)